
Know Where You Stand — And Where You Need to Go
Most organisations know they need to comply with data protection law. Far fewer know how far along they actually are. Assura’s Maturity Assessment gives you a clear, structured answer.Powered by the TR2UST Framework — a comprehensive compliance model covering 6 domains and 34 controls — the assessment evaluates your organisation across every area that matters: governance, rights management, data lifecycle, information security, third-party oversight, and incident response.As you assess each control, Assura calculates your overall maturity score and assigns a maturity level — from Reactive through to Optimised. You see exactly which domains need attention, which controls are pending, and what your next steps should be.
Key Capabilities
- 6 compliance domains with weighted scoring (Governance, Rights & Consent, Data Lifecycle, Information Security, Third-Party Management, Incident & Breach Management)
- 34 individual controls to assess, each with clear guidance
- Automated maturity level calculation (Reactive, Developing, Defined, Managed, Optimised)
- Visual domain-level dashboards showing progress at a glance
- Exportable reports for board presentations and regulator submissions
Know Who's Handling Your Data — And Whether They're Doing It Right
Every third-party vendor that processes personal data on your behalf is your responsibility. If they mishandle data, you bear the regulatory consequences. Yet most organisations have no structured way to assess, track, and manage vendor risk.Assura’s Vendor Management module gives you a centralised register of every third-party processor, with built-in due diligence assessments, contract tracking, and risk scoring. From initial registration through ongoing monitoring, you have full visibility into your vendor ecosystem.
Key Capabilities
- Vendor registration with company details, country of registration, certifications held, and service descriptions
- Lifecycle stage tracking: Prospect, Active, Under Review, Terminated
- Due diligence assessments with status tracking and assessment history
- Contract management tab for data processing agreements
- Certification tracking: ISO 27001, SOC 2 Type II, PCI-DSS, HIPAA, GDPR Compliant, and more
- Risk & Review tab for ongoing vendor oversight
Handle Every Request. Meet Every Deadline.
When someone asks for a copy of their data, requests deletion, or objects to processing, you’re legally required to respond — usually within 30 days. Tracking these requests by email or spreadsheet is a compliance risk waiting to happen. Assura’s DSR module provides a structured 6-step workflow to log, verify, search, and respond to any type of data subject request. The system supports all major request types recognised across Caribbean jurisdictions — from standard access and erasure requests to jurisdiction-specific rights like blocking (Jamaica/Cayman) and preventing harmful use (Jamaica).
Supported Request Types
Access Request, Rectification, Erasure, Blocking, Restriction, Portability, Objection, Prevent Processing, Marketing Opt-Out, Automated Decision Review, Withdraw Consent, Complaint, and more.
Key Capabilities
- 6-step workflow: Request Info, Requester Details, Verification, Data Search, Response, Review
- 13+ request types covering all major Caribbean data protection rights
- Priority levels and assignment tracking for team-based management
- Deadline tracking to ensure timely responses within legal requirements
- Complete audit trail for every request from receipt to closure.

Document Every Processing Activity — Clearly and Completely
Maintaining a record of processing activities isn’t optional — it’s a core requirement under virtually every data protection law. But building and maintaining one from scratch using spreadsheets is time-consuming and error-prone.
Assura’s ROPA module walks you through a structured 7-step process to capture everything a regulator would expect: what data you process, why, on what legal basis, where it’s stored, who it’s shared with, and how it’s protected.Each record is tied to a specific entity and department, making it easy to build a comprehensive, organisation-wide picture of your data processing landscape.
Key Capabilities
- 7-step guided workflow: Basics, Data Collected, Legal Basis, Data Sources, Data Sharing, Systems & Security, Review
- Entity and department-level organisation for multi-entity businesses
- Record types supported: Paper, Digital, or Both
- Draft and save functionality — complete records at your own pace
- Full audit trail for regulator accountability
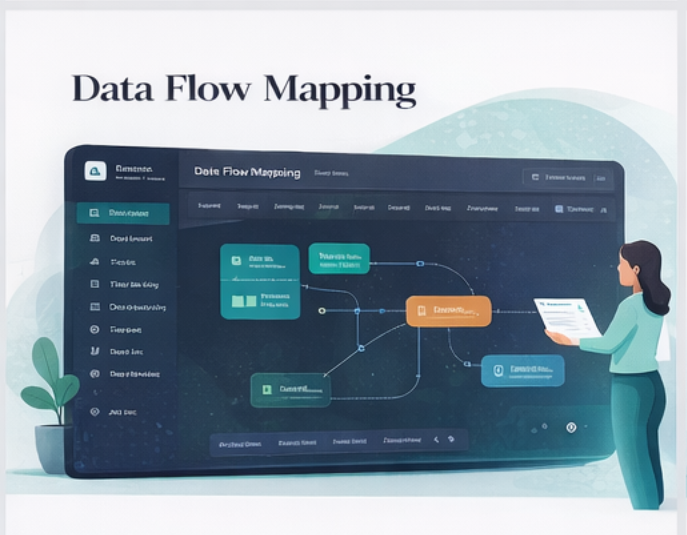
See Your Data in Motion
Key Capabilities
- Interactive visual canvas with drag-and-drop node placement
- Node types: Data Subjects, Processing Activities, Storage Systems, Transfers
- Risk indicators (Low, Medium, High) displayed on each node
- Cross-border transfer identification and flagging
- ROPA import to auto-populate flows from existing records

Respond to Incidents Faster — With Confidence
When a data breach happens, the clock starts ticking. You need to assess severity, determine notification obligations, and document everything — often within 72 hours. Panic and spreadsheets won’t cut it.Assura’s Breach Management module guides you through a structured 9-step response workflow. From initial reporting through classification, cause analysis, impact assessment, and remediation — every step is captured and documented.The built-in risk assessment uses fuzzy logic to evaluate breach severity across five dimensions: data sensitivity, volume of records, ease of identification, vulnerability of subjects, and containment effectiveness. The result is a quantified risk score with a severity-likelihood matrix and recommended regulatory action — so you know exactly what to do next.
Key Capabilities
- 9-step breach workflow: Initial Report, Classification, Cause, Data Affected, Response, Risk Assessment, Notifications, Remediation, Review
- Fuzzy logic risk scoring across 5 dimensions with composite scoring
- Severity x Likelihood matrix with automatic risk classification
- Recommended regulatory actions (e.g., notify DPA within 72 hours, consider data subject notification)
- DPO override capability for professional judgment adjustments
- Regulator-ready breach notification reports
